A Beginner’s Guide to Embedded Systems and IoT: Concepts, Architecture, and Real-World Applications
Introduction to Embedded Systems and IoT
Embedded Systems and the Internet of Things (IoT) are two closely related technologies that power much of the smart world around us. From automatic washing machines to smart home assistants, these systems work quietly in the background to make our lives easier. A beginner stepping into electronics, computer science, or related fields, understanding these concepts is essential because they form the backbone of modern intelligent systems.
What is an Embedded System?
An embedded system is a specialized computing system designed to perform a specific function or a set of functions within a larger system. Unlike general-purpose computers such as laptops, embedded systems are task-oriented and optimized for efficiency, reliability, and cost.
Examples include:
- Microwave ovens controlling cooking time and power
- Anti-lock braking systems (ABS) in vehicles
- Digital thermometers
These systems typically consist of hardware (microcontroller, sensors) and software (firmware) working together seamlessly.
Key Characteristics of Embedded Systems
Embedded systems have several unique characteristics that distinguish them from general computing systems:
- Dedicated Functionality: Designed for specific tasks
- Real-Time Operation: Must respond within strict timing constraints
- Resource Constraints: Limited memory, processing power, and energy
- Reliability: Expected to operate continuously without failure
- Low Power Consumption: Important for battery-operated devices
Understanding these features helps students design efficient systems tailored to real-world applications.
Components of an Embedded System
A typical embedded system consists of the following components:
- Microcontroller (MCU): The brain of the system that executes instructions
- Sensors: Devices that collect data from the environment (temperature, pressure, light)
- Actuators: Components that perform actions (motors, LEDs)
- Memory: Stores program instructions and data
- Communication Interfaces: Enable interaction with other devices (UART, SPI, I2C)
- Power Supply: Provides necessary energy to operate the system
Each component plays a critical role in ensuring the system functions correctly.
What is the Internet of Things (IoT)?
The Internet of Things refers to a network of interconnected devices that can collect, exchange, and act on data over the internet. These “things” include everyday objects like refrigerators, smartwatches, and industrial machines.
IoT extends embedded systems by enabling connectivity, making devices smarter and more interactive.
Core Elements of IoT Systems
An IoT system is typically composed of:
- Devices/Sensors: Collect real-world data
- Connectivity: Communication via Wi-Fi, Bluetooth, Zigbee, or cellular networks
- Data Processing: Cloud or edge computing systems analyze data
- User Interface: Mobile apps or dashboards for user interaction
These elements work together to create a seamless smart ecosystem.
Relationship Between Embedded Systems and IoT
Embedded systems are the building blocks of IoT. Every IoT device contains an embedded system that performs sensing, processing, and communication tasks.
For example:
- A smart thermostat uses an embedded system to measure temperature and adjust settings
- IoT connectivity allows users to control it remotely via a smartphone
Thus, IoT can be seen as an extension of embedded systems with added connectivity and intelligence. Figure 1 illustrate the difference between a standalone embedded system and an embedded system with IoT devices.
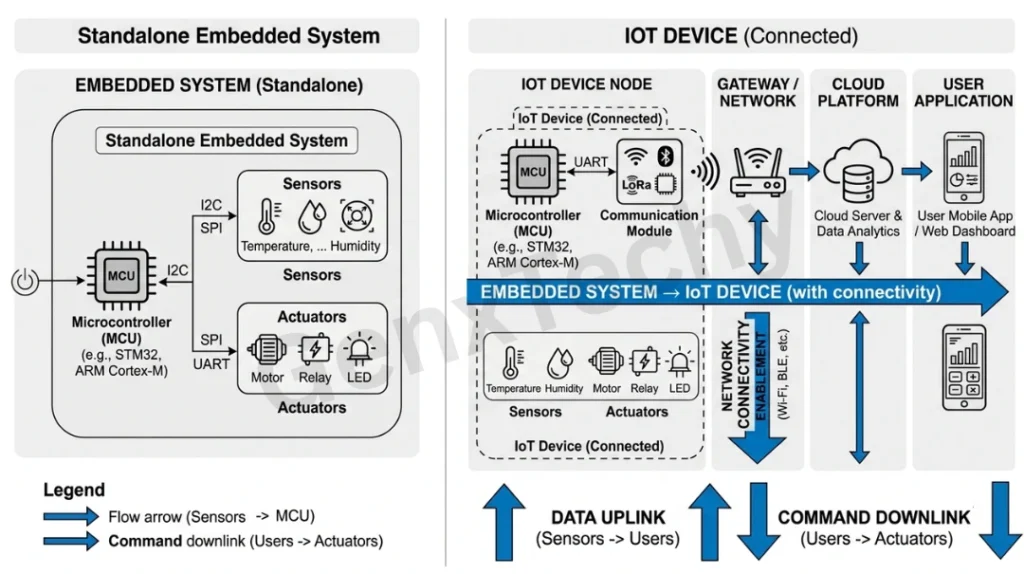
Fig. 1: difference between a standalone embedded system and an embedded system with IoT devices
Architecture of IoT Systems
IoT architecture is usually divided into layers:
- Perception Layer: Includes sensors and actuators that interact with the environment
- Network Layer: Handles data transmission via communication protocols
- Processing Layer: Processes data using cloud or edge computing
- Application Layer: Provides services like smart homes, healthcare monitoring, etc.
This layered architecture simplifies system design and enhances scalability. Figure 2 shows the different layers of an IoT Systems.
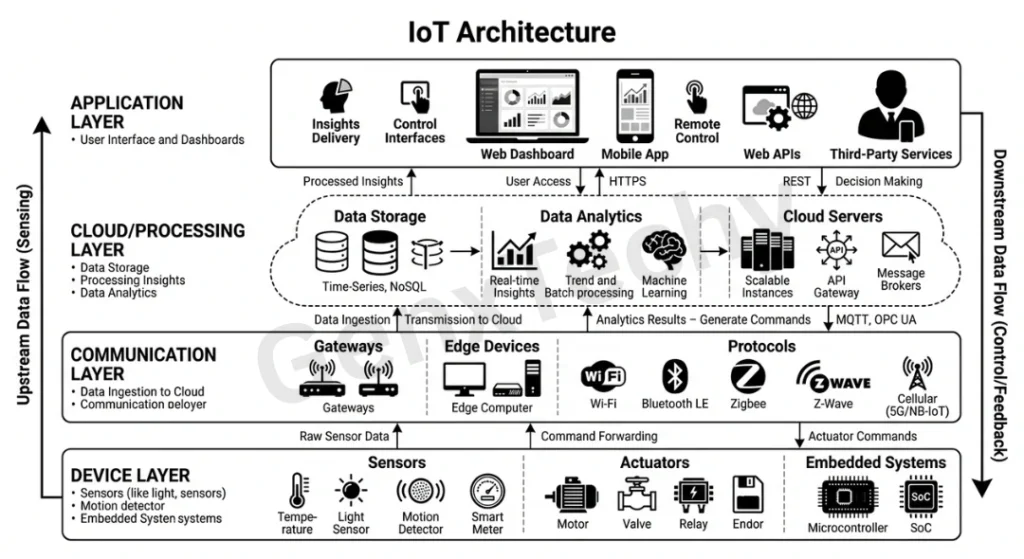
Fig. 2: Architecture of IoT Systems
Types of Embedded Systems in IoT
Embedded systems used in IoT can be categorized as:
- Standalone Systems: Operate independently (e.g., digital clocks)
- Real-Time Systems: Perform tasks within strict deadlines (e.g., airbag systems)
- Networked Systems: Connected via networks (e.g., smart home devices)
- Mobile Embedded Systems: Used in portable devices (e.g., fitness trackers)
Each type has unique design requirements and applications.
Communication Protocols in IoT
Communication is the backbone of IoT. Common protocols include:
- Wi-Fi: High data rate, widely used in homes
- Bluetooth: Short-range, low power communication
- Zigbee: Low power, suitable for sensor networks
- MQTT (Message Queuing Telemetry Transport): Lightweight protocol for IoT
- HTTP/HTTPS: Used for web-based communication
Choosing the right protocol depends on range, power, and data requirements.
Sensors and Actuators in IoT
Sensors and actuators are essential components:
- Sensors: Convert physical parameters into electrical signals
- Temperature sensors
- Motion sensors
- Light sensors
- Actuators: Convert electrical signals into physical actions
- Motors
- Relays
- Buzzers
Together, they enable IoT devices to interact with the physical world.
Role of Microcontrollers and Microprocessors
Microcontrollers (like Arduino, PIC) are widely used in embedded systems due to their low cost and power efficiency. Microprocessors (like Raspberry Pi) offer higher processing capabilities and are used in more complex IoT applications.
Key differences:
- Microcontrollers: Integrated, low power, real-time
- Microprocessors: High performance, flexible, supports OS
Embedded Software and Firmware
Software is what brings embedded systems to life. It includes:
- Firmware: Low-level software stored in memory
- Real-Time Operating Systems (RTOS): Manage tasks efficiently
- Application Software: Implements specific functionalities
Programming languages commonly used:
- C and C++
- Python (for IoT applications)
- Embedded C
Cloud Computing in IoT
Cloud platforms play a major role in IoT by storing and processing large amounts of data. Examples include AWS IoT, Microsoft Azure IoT, and Google Cloud IoT.
Benefits:
- Scalable data storage
- Remote access
- Advanced analytics
- Machine learning integration
Edge Computing in IoT
Edge computing processes data closer to the source rather than sending it to the cloud. This reduces latency and improves real-time performance.
Applications:
- Autonomous vehicles
- Industrial automation
- Smart surveillance systems
Security Challenges in IoT
IoT systems are vulnerable to various security threats:
- Unauthorized access
- Data breaches
- Device hacking
Solutions include:
- Encryption techniques
- Secure communication protocols
- Authentication mechanisms
Security is a critical area of research in IoT.
Applications of Embedded Systems and IoT
These technologies are widely used across industries:
- Smart Homes: Automated lighting, security systems
- Healthcare: Wearable devices, remote monitoring
- Agriculture: Soil moisture sensors, automated irrigation
- Industry (IIoT): Predictive maintenance, automation
- Transportation: Smart traffic systems, connected vehicles
These applications demonstrate how embedded systems and IoT improve efficiency and convenience.
FAQs
Explain how security challenges arise in IoT-based embedded systems.
Security Challenges in IoT-based Embedded Systems:
- Resource Constraints: Limited memory, processing power, and energy restrict implementation of strong security mechanisms.
- High Connectivity Exposure: Internet connectivity makes devices vulnerable to remote attacks and unauthorized access.
- Weak Authentication: Use of default passwords and poor access control increases security risks.
- Insecure Firmware Updates: Lack of secure or regular updates leaves devices exposed to known vulnerabilities.
- Poor Network Security: Unencrypted communication can lead to data interception and attacks like MITM.
- Physical Accessibility: Devices deployed in open environments can be tampered with easily.
Why are IoT-based embedded systems more vulnerable than traditional systems?
IoT devices are more vulnerable because they have limited resources, are always connected to the internet, and often lack strong security mechanisms like encryption and authentication.
Illustrate the trade-off between reliability and flexibility in embedded systems.
Trade-off between Reliability and Flexibility in Embedded Systems:
- Definition of Reliability: Ability of the system to operate consistently without failure under defined conditions.
- Definition of Flexibility: Ability to adapt to new functions, updates, or changing requirements.
- Fixed vs Configurable Design: Highly reliable systems use fixed, well-tested designs, while flexible systems allow modifications, which may introduce errors.
- Complexity Impact: Increasing flexibility adds software/hardware complexity, which can reduce reliability due to higher chances of bugs and failures.
- Update vs Stability: Flexible systems support frequent updates and upgrades, but each update may affect system stability and reliability.
- Resource Constraints: Adding flexibility requires more memory and processing, which may stress limited resources and impact reliable performance.
- Trade-off Conclusion: A balance is required—critical systems (e.g., medical or automotive) prioritize reliability, while consumer devices may favor flexibility.
Explain the role of connectivity in transforming a standalone embedded system into an IoT device.
Role of Connectivity in Transforming a Standalone Embedded System into an IoT Device:
- Data Exchange Capability: Connectivity (Wi-Fi, Bluetooth, Zigbee, cellular) enables the embedded system to transmit and receive data beyond its local environment.
- Remote Monitoring: Users can observe device status and performance in real time through mobile apps or web dashboards, unlike standalone systems.
- Remote Control and Operation: Devices can be operated from anywhere, allowing actions such as switching, configuration, or scheduling remotely.
- Cloud Integration and Data Analytics: Connectivity allows data to be sent to cloud platforms where it can be stored, processed, and analyzed for insights and decision-making.
- Real-Time Updates and Maintenance: Firmware updates, bug fixes, and configuration changes can be applied over-the-air (OTA), improving system performance and security.
- Inter-device Communication: Connected systems can interact with other IoT devices to enable coordinated and automated actions (e.g., smart home automation).
- Scalability and System Expansion: Connectivity allows multiple devices to be integrated into larger networks, making the system scalable and adaptable.
- Enhanced Intelligence: By leveraging cloud/edge computing, connected systems can perform intelligent decision-making and predictive operations.
Connectivity acts as a bridge between physical embedded systems and the digital world, transforming isolated devices into smart, interactive, and intelligent IoT systems.
How do AVR microcontrollers achieve high processing speed and low power consumption simultaneously?
- RISC Architecture: AVR microcontrollers use a Reduced Instruction Set Computing (RISC) architecture, where most instructions execute in a single clock cycle, ensuring fast processing.
- Harvard Architecture: Separate memory spaces for program and data allow simultaneous access, increasing execution speed.
- Efficient Instruction Set: Simple and optimized instructions reduce execution time and improve overall efficiency.
- Low Clock Cycle Operations: Many operations complete in one cycle, reducing active processing time and hence saving power.
- Power-saving Modes: AVR controllers support multiple sleep modes (Idle, Power-down, Standby) to minimize energy consumption when the system is inactive.
- Clock Management: Ability to adjust clock frequency dynamically helps balance speed and power consumption based on application needs.
- On-chip Integration: Built-in peripherals (timers, ADC, communication modules) reduce the need for external components, lowering power usage.
- Efficient CMOS Technology: Fabrication using low-power CMOS technology ensures minimal power dissipation.
- Fast Wake-up Time: Quick transition from sleep mode to active mode allows efficient power management without compromising responsiveness.
AVR microcontrollers achieve a balance between high speed and low power through optimized architecture, efficient instruction execution, and advanced power management features.
What is a Man-in-the-Middle (MITM) attack in IoT?
A Man-in-the-Middle (MITM) attack occurs when an attacker secretly intercepts communication between two IoT devices or between a device and a server.
- Interception of Data: The attacker positions themselves between the sender and receiver to capture sensitive data such as passwords, sensor data, or commands.
- Data Manipulation: The attacker can alter or inject false data without the knowledge of either communicating party.
- Common Cause: Often occurs due to lack of encryption or insecure communication protocols in IoT systems.
- Impact: Leads to data breaches, unauthorized control of devices, and compromised system integrity.
What is a botnet in IoT security?
A botnet is a network of compromised IoT devices that are infected with malware and controlled remotely by an attacker (called a botmaster).
- Formation: Attackers exploit weak security (default passwords, unpatched firmware) to gain control over multiple IoT devices.
- Remote Control: These infected devices (bots) receive commands from a central server without the user’s knowledge.
- Purpose: Commonly used to launch large-scale attacks such as Distributed Denial-of-Service (DDoS), spam distribution, or data theft.
- Impact: Degrades network performance, disrupts services, and compromises security of systems connected to the network.
What role does connectivity play in IoT security risks?
Role of Connectivity in IoT Security Risks:
- Increased Attack Surface: Connectivity (Wi-Fi, Bluetooth, internet) exposes devices to external networks, making them accessible to attackers.
- Remote Exploitation: Attackers can target devices from anywhere without physical access, increasing the risk of hacking.
- Protocol Vulnerabilities: Weak or insecure communication protocols can be exploited to intercept or manipulate data.
- Data Exposure: Continuous data transmission over networks increases the chances of data leakage if not properly encrypted.
- Unauthorized Access: Poorly secured connections can allow intruders to gain control over IoT devices.
